Every time another cyber security breach occurs in the financial industry, it reduces consumer and corporate confidence in how well their data is being protected.
The risk to institutions is grave and manifold, ranging from the loss of sensitive customer data to the exposure of corporate intellectual property and confidential business plans being accessible to criminals after their initial penetration of the digital mortgage point-of-sale entry point.
If it’s been a while since you’ve considered current security threats, let alone evaluated the protections you now have in place, it’s worth looking at the failures of other institutions as cautionary tales.
This is especially the case in context of the novel coronavirus pandemic and rising COVID-19 infections. The pandemic is associated with a 238% increase in cyber attacks focused on banks, according to ZDNET.
It noted that VMWare Carbon Black’s latest Modern Bank Heists report indicates data breaches increased between February and April 2020, just when COVID-19 began making its way around the world. “The cyber security firm’s research, which includes input from 25 CIOS at major financial institutions, adds that 80% of firms surveyed have experienced more cyber attacks over the past 12 months, an increase of 13% year-over-year.”
Whether it’s an attack on data in a POS setup or on servers used to store enormous quantities of sensitive information and to process and evaluate banking decisions, the threat is growing and you and fellow stakeholders at your organization need to stay on top of the possibility of weakness in your own computing system.
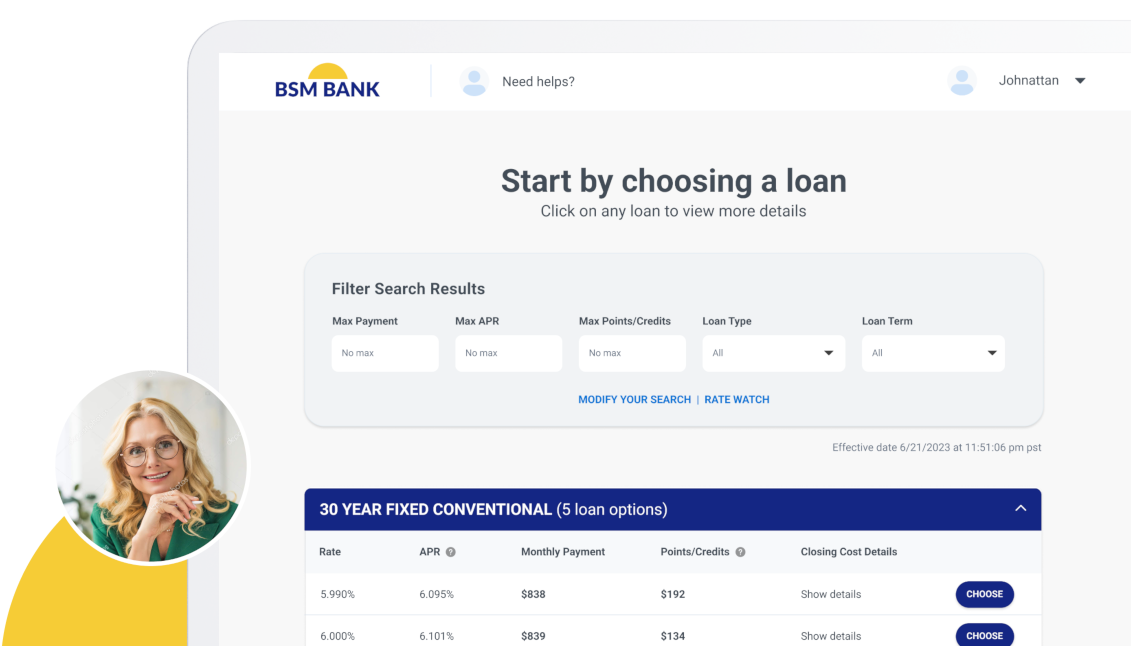
This underscores the necessity of working with software developers that have a demonstrable record of following current industry best practices for cyber security in mortgage technology, such as the team at BeSmartee. Keeping that in mind, here’s a look at some recent POS and banking cyber crimes and their fallout.
Evil Corp
Back in December 2019, the United States Treasury Department went after a group of cybercriminals based in Russia known as Evil Corp. This group is charged with forcing its way into the systems of 300 banks and other financial institutions across more than 40 countries, according to a report in the ABA Banking Journal. The result was at least $100 million in theft, per the U.S. Treasury.
How are banks supposed to protect themselves and customers given the evolving nature of the capabilities of hacker groups? ABA Banking Journal stated that, “As the scale of such breaches seems to only soar, banks are hiring their own specialty teams or contracting with vendors, all of whom have one mission: think like a constantly changing set of globally active bad actors.”
Beyond getting into the mindset of these criminals, “More banks are now both running formal attack simulations on their own systems and a few are working with actual hackers—the non-criminal or “white hat hackers,” anyway—at various scales, seeking to benefit from the mindset that inspires the banking industry’s own cyber-invaders.”
If you don’t have a full-fledged security department with cybercrime experience now, you will want to bring in consultants and work with third party software security professionals to make sure your own POS and other systems are adequate to meet the rising threats of online criminals now, before your institution becomes another statistic.
Major Same-Day Malware Attacks at POS Systems
POS systems are certainly an attractive target to criminals looking for a quick way to grab data they can use to drain finances from accounts and steal personal details to conduct identity theft. Cyber Security Hub reported on three separate companies whose POS systems were attacked during the same week in December 2019.
Subscribe to BeSmartee 's Digital Mortgage Blog to receive:
- Mortgage Industry Insights
- Security & Compliance Updates
- Q&A's Featuring Mortgage & Technology Experts
POS malware was discovered in the servers for processing payments at the retail giant Wawa, which has POS equipment at 850 locations. Investigators found that malware had been installed on the company’s servers approximately 9 months before discovery.
Also in December, Champagne French Bakery Cafe revealed that it found malware installed on POS devices, used to capture cardholder names and other details plus the internal code for verification, between February 18 to September 2019. Hamburger restaurant chain Islands also reported in December that malware had been found in POS terminals at 50 stores in multiple states.
The growing ability of criminals to penetrate large POS systems like these illustrates the fact that financial institutions should be taking risk seriously, evaluating if their own systems are capable of providing the needed protection.
Capital One
An individual software engineer based in Seattle managed to hack into a server of Capital One, stealing personal information on more than 100 million individuals, as reported by the New York Times in July 2019. It’s been dubbed one of the biggest thefts ever of data from a financial institution. Fortunately for investigators, the criminal in question was not very savvy about protecting herself from law enforcement. She had gone online leaving boastful comments about her hacking. At this point, agents from the FBI tracked her to the online forum Meetup.
Approximately 140,000 social security numbers plus 80,000 bank account numbers were stolen during the breach. What’s more, Canadian social insurance numbers for one million citizens were also taken. Cleaning up the data breach will cost an estimated $150 million. This includes paying for credit monitoring services for all customers affected. These sobering numbers should encourage banking professionals to take their own internal security more seriously and to conduct internal audits to seek out any weaknesses.
Bank of America
When you are one of the preeminent digital lending companies in the nation, it’s of the utmost importance to shore up computer networks in this era of cybercriminal attacks. A major breach occurred on April 22, 2020 at the Bank of America. Data on clients was exposed after Bank of America uploaded details from Paycheck Protection Program applicants to a test platform maintained by the Small Business Administration, according to InfoSecurity.
The idea was that banks would try out submitting information for PPP loans, testing the system before an anticipated second period of applications began. Stolen information included details about specific businesses as well as their owners. Business addresses, tax identification numbers, social security numbers, phone numbers and email addresses and even the citizenship status of applicants.
Bank of America had processed at least 305,000 applications with the SBA for PPP relief. Once BoA learned of the penetration, it notified the SBA, asking the administration to shore up the exposed information. While there is no evidence that criminals were able to take and use the details, the bank is now offering clients a two-year membership in an identity theft protection program run by Experian.
When Was the Last Time You Evaluated the Security Protecting Your Computer System?
With so many instances of data breaches affecting financial institutions, it makes sense to take a good hard look at the security you have in place now to protect sensitive data, from digital mortgage details for customers to internal company intelligence.
If you’re currently working with an outdated POS or are now actively looking for a safe and robust point of sales setup to make your business processes more efficient, you’ll get better results when you team up with professional software developers with years of experience in the industry.
To learn more about the security underpinning our mortgage POS software, please give us a call at (888) 276-1579 or reach out to our mortgage technology experts at sales@besmartee.com today.